The Pitfalls of Social Engineering and How You Will Avoid It
Social engineering attacks are not only becoming more frequent against businesses and SMBs but are also becoming more and more complex. Hackers are cr...
Read More →We use cookies to improve your experience on our site and to show you personalised advertising. Please read our cookie policy and privacy policy.

Social engineering attacks are not only becoming more frequent against businesses and SMBs but are also becoming more and more complex. Hackers are cr...
Read More →
Cyber-crime is continually evolving and inflicting a lot of damage to businesses and companies. It involves a host of malicious criminal practices des...
Read More →
The term "doxing" is derived from the word "document tracing" which means to retrieve documents about a particular person or company in order to lear...
Read More →
A cyber attack is any type of offensive maneuver that targets computer information systems, infrastructures, computer networks, or personal computer d...
Read More →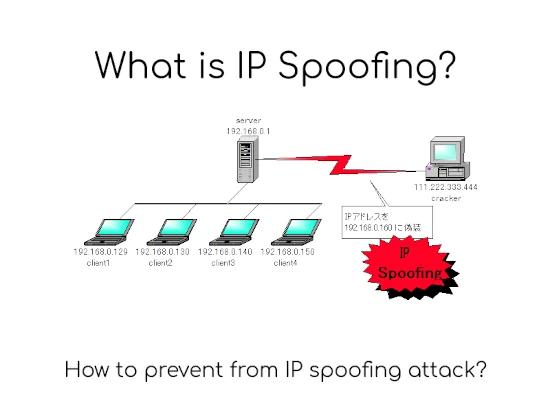
IP addressInternet Protocol address in short IP address is an identifier for a computer or device on a network. Any device connected to the IP network...
Read More →
Hackintosh is a portmanteau of the terms hacking and Macintosh. A Hackintosh is a type of non-Apple computer designed to run unauthorized versions of ...
Read More →
Computers have become mandatory for personal use or to run successful businesses. It is not enough to have isolated computers systems; they need to be...
Read More →
Many people are familiar with computers, tablets, smartphones, and wireless Internet. It's quite possible that there will be around 50 billion or more...
Read More →
When you're online, you expose your vulnerability to malicious virus that have been growing in virulence and ferocity over the last few years. The key...
Read More →
A backdoor can refer to a legitimate point of access embedded in a system or software program for remote administration. Generally a programmer may so...
Read More →