How New Software is Preventing the Spread of Indecent Imagery
The sharing and posting of indecent imagery online is an increasing concern in the UK. In this article, we’re going to be talking about the ways in wh...
Read More →We use cookies to improve your experience on our site and to show you personalised advertising. Please read our cookie policy and privacy policy.

The sharing and posting of indecent imagery online is an increasing concern in the UK. In this article, we’re going to be talking about the ways in wh...
Read More →
A virtual core is a CPU with a separation between two areas of the processor. Virtual cores take on some of the processing of the computer without int...
Read More →
In today's world, Blockchain technology serves as the perfect example of a rising technology being used to boost local commerce and peer-to-peer inter...
Read More →
When the attackers' of WannaCry ransomware sprang into action, it held victims hostage by encrypting their data and demanding money in bitcoins to reg...
Read More →
IPv6 (Internet Protocol version 6) is the most recent version of the Internet Protocol. It is a network layer protocol that enables data communication...
Read More →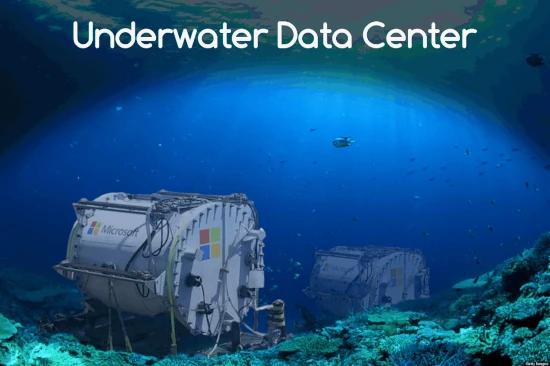
A radical new experiment from Microsoft brings a change and a new level of thinking. The software giant's underwater data center trials have attracted...
Read More →
Bitcoin paved the way with its cryptographically stored ledger, scarce-asset model, and peer-to-peer technology. These features provide a starting poi...
Read More →