Navigating Cyber Threats: Enhancing Security With Reverse a WHOIS Lookup
The contemporary digital realm is heavily laden with cyber threats, presenting substantial obstacles for both companies and individuals. In 2023, a no...
Read More →We use cookies to improve your experience on our site and to show you personalised advertising. Please read our cookie policy and privacy policy.

The contemporary digital realm is heavily laden with cyber threats, presenting substantial obstacles for both companies and individuals. In 2023, a no...
Read More →
In the fascinating intersection of psychology and technology, there exists a formidable adversary that exploits both human vulnerability and digital l...
Read More →
The simple fact that you rely on electronic devices to help run your business puts you at risk of a cyber attack. Since a significant percentage of th...
Read More →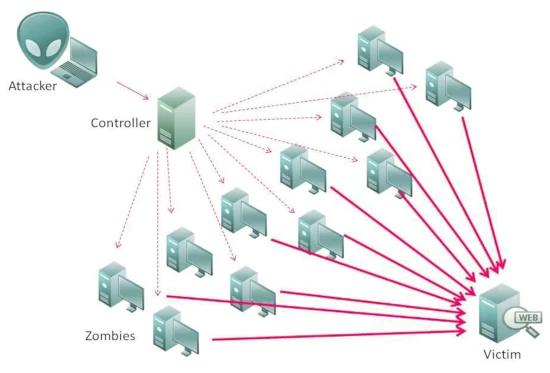
In the digital age, distributed denial of service (DDoS) attacks have become a prevalent and concerning form of cyber threat. These attacks can disr...
Read More →
Cyber-attacks and data breaches have become increasingly ubiquitous in recent years. Now more than ever, having cybersecurity tools such as antivirus ...
Read More →
The digital age has brought about numerous conveniences, but it has also given rise to new forms of cybercrime. One of the most prevalent and deceptiv...
Read More →
The past year has been one of the most notable years in cybersecurity. It has broken all records in cyberattack statistics. The number of companies, o...
Read More →
Social engineering attacks are not only becoming more frequent against businesses and SMBs but are also becoming more and more complex. Hackers are cr...
Read More →
A cyber attack is any type of offensive maneuver that targets computer information systems, infrastructures, computer networks, or personal computer d...
Read More →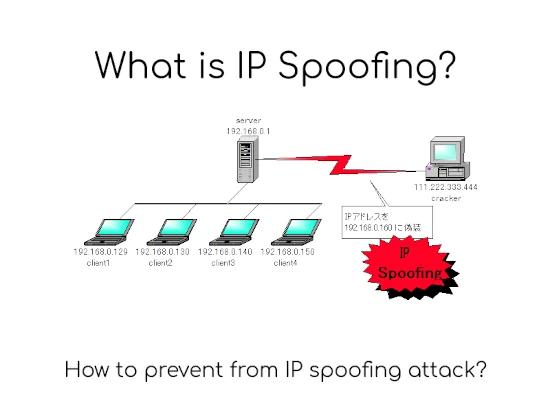
IP addressInternet Protocol address in short IP address is an identifier for a computer or device on a network. Any device connected to the IP network...
Read More →