Social Engineering Attacks and Identity Theft
In the fascinating intersection of psychology and technology, there exists a formidable adversary that exploits both human vulnerability and digital l...
Read More →We use cookies to improve your experience on our site and to show you personalised advertising. Please read our cookie policy and privacy policy.

In the fascinating intersection of psychology and technology, there exists a formidable adversary that exploits both human vulnerability and digital l...
Read More →
Are you searching for entertaining and captivating first thread post ideas for your blog? Do you desire to make your readers burst into laughter an...
Read More →
In a world where technology is changing how we live our daily lives, facial identification stands out as a groundbreaking innovation that seamlessly c...
Read More →
In the ever-evolving digital landscape, local businesses cannot afford to overlook the power of local SEO. Harnessing its potential can lead to increa...
Read More →
We all crave security in our homes and businesses. But how do we choose the right solutions aimed at guaranteeing it? The market's flooded with securi...
Read More →
With the advent of a plethora of handheld devices such as tablets, smartphones and other digital devices. Different devices support different video fo...
Read More →
You're always on the hunt for ways to boost your business's bottom line, aren't you? You've heard whispers in the industry about a technique called wh...
Read More →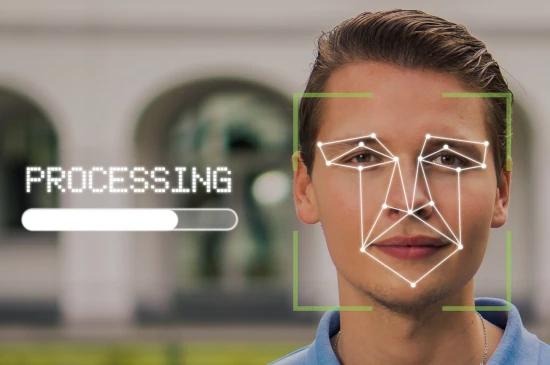
With the incorporation of KYC verification, companies may lower the chances of illegal financial activities while adhering to global norms. Moreover, ...
Read More →
In the modern age, it is essential for businesses to ensure that they have a powerful online presence. It is necessary to optimize a website for searc...
Read More →
Digital identity is truly established as the most considerable technology trend on the face of the Earth. Consequently, a revolution in how people int...
Read More →